Everything posted by Sensei
-
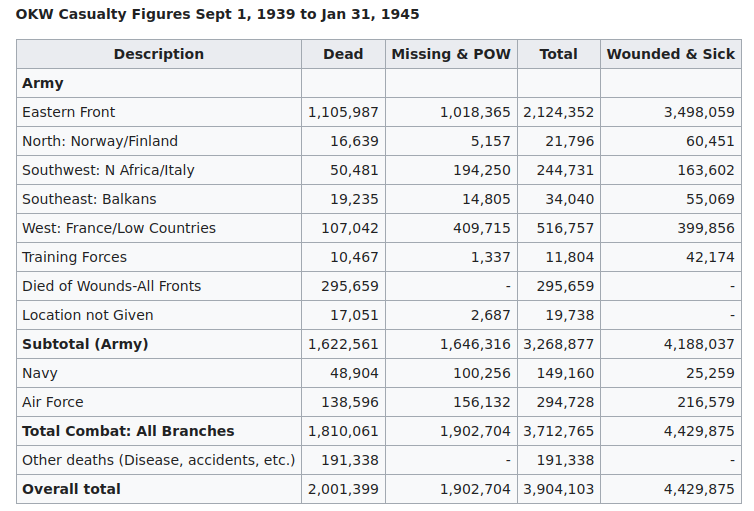
The West has no ability to win now.
-
is 2% considered to be safe or risky?
"The dose makes the poison" https://en.wikipedia.org/wiki/The_dose_makes_the_poison Everything is poison and nothing is poison, depending on the amount of..
-
Physics - friction class...
This is experimental physics - you take a tire, perform an experiment and get results that are put on a graph. And a few such repetitions and averaging them produces a graph that extrapolates to the rest. BTW, Formula One drivers like warm tires: https://www.google.com/search?q=formula+one+driver+like+warm+tires "warmer tyres are grippier on the tarmac and that is essential when driving a car which can be chucked around corners at 190mph. When lining up on the grid before the start of a race, the tyres are wrapped up in covers – acting almost like a blanket – in order to preserve as much heat in them as possible." A typical F1 driver uses 3 sets of tires for the main race. "On a standard weekend, drivers are given 13 sets of dry weather tyres, four sets of intermediates and three sets of full wets. An extra set of softs is reserved for those who reach Q3, while all drivers must use at least two different slick compounds in the race, providing the track is dry." "Street car tyres will last about 15,000 Km, but the life of an F1 tyre is between 60 and 120 Km. Since they are built for extreme performance at high speeds, the rubber wears off in no time. This is why team personnel rack their brains to change the tyres at the appropriate moment of the race and in minimum time."
-
In the age of Artificial Intelligence, what should be free?
AI source code is one thing, and a database of what AI has learned is another. A regular John Doe (mentioned by Airbrush) would not be able to teach his own AI @ home everything that, for example, ChatGPT or other AIs from other global IT companies have learned their implementations. It would require writing a custom search engine crawler, enormous amount of storage, powerful computer infrastructure ("server room"), fast fiber Internet, multi-millions of dollars to run this stuff etc.. A hacker/programmer would not need AI assistance at all to commit such crimes.. If an evil hacker created his own artificial intelligence without limits like Airbrush wanted, it would certainly be available only on the dark web, i.e. an ordinary John Doe still would not have access to it (invitation-only, expensive, paid cryptocurrencies, etc.).. If John Doe can access dark web, would rather hire someone to do everything ("dirty job") for him.. Note. Muslim terrorists have everything handed to them on a plate - instructions on how to do everything are publicly available even on Wikipedia, and most of them are unable to do anything with it.. An artificial intelligence instructing them how to make a bomb would be as useful to them as English textbooks with these information which they have right now access to but still unable to proceed..
-
In the age of Artificial Intelligence, what should be free?
IT companies own the artificial intelligence they have created. If someone asks Google's or Bing search engine or artificial intelligence "how to hide a body" or "where to find zoophilia?," a trail is left in the IT infrastructure that can be used against the person seeking for such kind of information.. Undoubtedly, administrators of public search engines are alerted when someone searches for such keywords..
-
functions
https://en.wikipedia.org/wiki/Function_(mathematics) https://en.wikipedia.org/wiki/Function_(computer_programming)
-
Optimizing Quick Sort Algorithm for Efficiency and Best Practices
1) make function that will dynamically generate arrays with random values and random size 2) create a function that will check if the array is correctly sorted 3) create a loop that will generate arrays, sort them and check if they are correctly sorted and warn you if they don't match (dump unsorted array to know in what circumstances it failed!) 4) run it millions of times e.g. overnight Programmers call it "unit testing": https://en.wikipedia.org/wiki/Unit_testing
-
Optimizing Quick Sort Algorithm for Efficiency and Best Practices
https://www.google.com/search?q=python+recursion+limit "Python has a default maximum recursion depth of 1000" As you can see, this is much worse than, for example, in C/C++ on Windows, where you have a default of 1 MB per thread. You should create a special debugging version that prints the current level of recursion and/or calculates the maximum depth it has reached so you can calculate at what number of elements in the array problems will occur.
-
Can I delete such folders from C disk, example "02eeb6d92f89e33ba2ea06"
..three weeks ago I told you to use FileMon or modern alternatives..
-
Is there a simple way to send phone messages to PC
IMHO the simplest/easiest way would be to write your own smartphone app to do it.. Which model? Which OS version? Great. ..years, years ago I wrote such an application that exports SMS to CSV file.. then I find out that Google no longer allows you to upload such applications that read/write SMS to the Google Play Store, so project was cancelled and remains only on my obsolete disks.. Start from learning about adb https://developer.android.com/tools/adb It can upload files to the device, download files from the device https://www.google.com/search?q=adb+read+text+messages
-
AI and the actors strike
Face book is a sufficient source of all kinds of faces.. and they will do it for free.. Studios, as well as ordinary artists, since it can be downloaded for free, have access to the motion capture database with bone or face movements. Once recorded, the movement of an actor/stuntman in a special suit can be reused millions of times at any time. https://www.google.com/search?q=motion+capture ..which, of course, reduced the need for real paid experienced stuntmen.. George Lucas started shooting Star Wars in the middle of the series, due to the inability to pay stuntmen or generate so many "clones" in the first 3 episodes.
-
Any clairvoyants on A.I. here ?
God-mode.. predicting the future..
-
sunlight fades colors?
I think a good search engine keyword would be "organic and inorganic dyes and decomposition under sunlight", "organic and inorganic dyes and degradation under sunlight", or "photocatalytic degradation of dyes". I immediately received several articles.
-
I see. All of my posts go into 'trash can'. That, itself, is interesting to me
Start writing sensible things, and they won't end up in the trash.. You can measure the speed of light at home.. laser rangefinder uses it to measure distance (e.g. a land surveyor uses it in the early stages of house construction).. The latency of your smartphone when you talk or send data over the Internet (such as now) is due to the speed of light. Just use ping in the terminal (cmd.exe) and see how it changes when you ping local city server, other country in the same continent server, or opposite end of the Earth. So, if you start a post with "it's a fake number", don't expect it to continue and waste people's time..
-
I would like to have a debate with someone that claims math is 'real'
1) math is abstract 2) In experimental physics, a scientist makes an observation of a physical system, assigns some initial state to it, waits a while (measures time), and then repeats the measurement. After a longer or shorter period of time, a database of results is created, which are analyzed and a mathematical function is created to "simulate", "predict" the result if the next time we find ourselves in the same or similar environment as during the experiment. The math is used to interpolate and extrapolate the data (i.e. fill in the gaps and make useful predictions).
-
New User Guide
...just like any new member who makes ambiguous claims...
-
Metronidazole - shouldn't we be concerned that the question of carcinogenic potential hasn't been settled?
One of your unique posts that I can agree with.. Drinking Technetium-99[m] is widely used medial technique.. https://www.google.com/search?q=Technetium-99[m]
-
New User Guide
Oh, those mortals.. You can pretend to be a mobile user by clicking ctrl-shift-m.. If you are annoyed by the fact that YouTube stops playing audio or video simply by switching to another application, on Android run YT in desktop mode.... ..different payloads..
-
Too many tangents (bots, trolls and socks, oh my!)
A company that trains a chat bot or has a crawler will download (visit) a website (such as a forum), all posts, recursively, usually much faster than any human can do it. A human has to sleep and has limited abilities to read text. A bot that scans the site does not. Some developers add some delay between downloads, others don't. Therefore, an analysis of the web server logs for a given IP address/ranges/db may show that it is some kind of bot or crawler, simply because there are too many requests from the same client IP address (or ASN IP ranges from the same company). Example bash script for a bot that will download the entire 1st topic page of scienceforums.net, and resemble a simple DoS attack: #!/bin/bash for TOPIC in {1..128952} do wget -q "https://www.scienceforums.net/topic/$TOPIC--/" done 128952 / one request per second = 36 hours to download entire scienceforums.net 1st topic page.. (if done from multiple IPs e.g. through Tor network (it has less than 2000 servers ATM), DDoS attack) Tor version: Installation: sudo apt install proxychains tor sudo service tor start Usage: #!/bin/bash for TOPIC in {1..128952} do proxychains wget -q "https://www.scienceforums.net/topic/$TOPIC--/" done 128952 / 2000 requests per second = (theoretically, doubtful this server will handle it) 65 minutes to download entire scienceforums.net 1st topic page.. (Tor switches end-IP address every 10 minutes) Going by comments, will obviously require much much more, and it will have requests like: "https://www.scienceforums.net/topic/$TOPIC--/?do=findComment&comment=$COMMENT" Your comment is one of the newest and has COMMENT=1244489 Downloading them all, will take 1244489/3600=346 hours (if one request per second).
-
Too many tangents (bots, trolls and socks, oh my!)
Of course, different companies use different IP ranges. For example, I have a database of all the end IP addresses of the Tor network. So when someone uses Tor or the Tor browser to visit my server, I can tell immediately. You can tell if a Google crawler has visited your web server simply by checking the IP address. (not single IP address, but Google ASN IP ranges) https://www.google.com/search?q=Google+ASN+IP+range Microsoft's Bing https://www.bing.com/toolbox/bingbot.json That it is a chatbot that is trained on scienceforums.net as a source? "Sometimes it’s hard to tell the difference between awkward phrasing you might get with a bot"
-
Too many tangents (bots, trolls and socks, oh my!)
Facepalm. C'mon.. make database of IP addresses..
-
Tridimensional image gadget... can anyone explain ?
...they want your money..
-
Can I delete such folders from C disk, example "02eeb6d92f89e33ba2ea06"
Its name consists of 11 bytes in hexadecimal numeral system. 11 bytes * 8 bits = 88 bits. Which is a typical length for a certain type of hash. https://en.wikipedia.org/wiki/Cryptographic_hash_function https://www.google.com/search?q=hash+"88"+bits+length Although it can shorten a hash with more bits to less, cutting part of it, to make it harder to figure out what it was prior modifications. The proper, untruncated, MD5 hash length should be 128 bits = 16 bytes = 32 characters in hex format. https://en.wikipedia.org/wiki/MD5 SHA-1, SHA-256 are longer. https://en.wikipedia.org/wiki/SHA-1 160 bits https://en.wikipedia.org/wiki/SHA-2 256 bits If you see such name on your drive, you should: 1) open regedit and search for this value either in ASCII and hexadecimal (byte) form. 2) use FileMon or equivalent to figure out which app opens and uses this folder: https://learn.microsoft.com/en-us/sysinternals/downloads/filemon 3) scan all content files for the existence of this name in some file. However, the chances of success are slim. I would simply rename it to something else (i.e. append suffix, prefix) and then see what happens. Is it recreated? Some app starts misworking?
-
is RFID blocking wallet a gimmick?
Ok. Now imagine. Hackers break to your smartphone, so their IP address, is equal to your IP address. And you complain about unauthorized transaction, is laughable. It happens from 1) your device 2) from your IP address 3) from your GPS.. 4) you were there at the time of dinner.. True investigation that you're not the real purchaser but fake would require taking monitoring data and comparison of data. If they have such.. Most people will just give up and become their loss.... ps. I see your reply was adjusted while I was in the middle.. so excuse me to not taking account your further thoughts..
-
is RFID blocking wallet a gimmick?
How can they differ from legal or illegal access? It is word from you vs word of bartender, where you get drunk.. ...you have no idea when and where somebody will make photo of your cards..