-
Does some numerology intersect with standard mathematics?
I wrote a conclusion to my thread before I read the most correct replies. I will try to respond to them in the next couple of days but until then I will explain why I started the thread. So I’ve presented a challenge to all you science types about numerology. Myself I don’t practice numerology. But that doesn’t mean patterns in all things don’t exist. I mean I can see where giving a name to a baby would influence their future. There was a case were a father named his son Sue so he would grow up to be tough because his father wouldn’t be there to look after him. Seriously though, I don’t think we can see all patterns. But why does this matter? I think if you have one pattern you can apply it to a place where we can’t see a pattern. In a previous thread I mentioned Sesquation could be used to solve for x in polynomials. In this case of polynomials I hypothesized that if you had test values of the graph the pattern that is known (Sesquation) would reveal a pattern. I don’t have all the details but I think there is something there. Cryptography has roots in numerology. Simple cyphers have letter frequencies. But I don’t try to predict the future with numerology. I am only concerned with the processing of the pattern. I wish I could share the numerology work an unknown reader sent me. It wasn’t to predict the future but related numbers of patterns found by a sieving algorithm. It looked sophisticated and I didn’t have anyway to debunk it. But also true numerology is dangerous. That is the misuse of. But I don’t completely rule out significant patterns. Take paintings for example. Heads are drawn in a triangle representing the trinity. So any designed creative work could possibly be explained by similar methods as numerology. I have exhausted this thread but a hope it give a thought provoking take on patterns. Because in public key cryptography you don’t have to find the pattern of the trap door function, you just have to find 2 or more unknowns based on a makeshift pattern you augmented the graph with. But that is speculation. But you have to start with speculation to start new investigations.
-
Does some numerology intersect with standard mathematics?
Wait a minute, I thought we set water at 100C for the fact that is were water boiled? The temperature system is defined by the scale we set. I’m just questioning when scientists set these scales does it resemble numerology? Yes the scale is usually based on something tangible, but why wouldn’t we have patterns in the intangible? It reminds me of Dungeons and Dragons. Skills are assigned a number and there is a dice roll. These mathematical machines produce actions that no math could explain. I mean the results are quantifiable but it works. What happens when WAGs produce patterns? I’m not saying there are patterns to everyone future. But I don’t rule it out. Because with a calendar may or not be arbitrary but it is a system man created so how can we rule out patterns we can’t see? And a calendar may very well have patterns because it is not arbitrary. It is based on the sun. To me the survey falls under D&D. That is assigning a result that isn’t a computational pattern. MigL calls them WAGs, but it is arguably close to numerology. My point is that we are doing it very often when trying to find new patterns. We just call it the function of f at x on the number line. I know numerology sounds illogical but what patterns can’t we see because we think it’s not scientific?
-
Does some numerology intersect with standard mathematics?
Numerology is the ancient esoteric belief that numbers carry energetic vibrations capable of revealing your personality, life path, and destiny. By calculating specific digits from your birth date and name, you can uncover a personal "blueprint" for self-discovery and life planning. [1, 2, 3] I agree from a logical sense predicting actions from words doesn’t seem possible. But again we are trying to explain everything else by numbers. Ten digits on hands; base ten. Humans are basically similar why wouldn’t there be numbers that describe us. Crypto was going to be my next example. But what about handwriting analysis? It is a science based on something that relates an action to personality. My own definition of numerology is to use math where traditional math could not express a logical, traditional pattern. One definition on the web defined as “meanings in numbers.” I have run into numerology before a couple of years ago when I got an email from someone who saw my semiPrime factoring work. I was not doing numerology, but this person had computer algorithms drawing relationships. I didn’t know how it worked but it seemed convincing by the fact the where similarities in numbers produced but no way of telling what they exactly meant. And then there is Stanislaw Lem. In The Futurelogical Congress , Lem describes present day scientists studying what new words will be in the future in order to predict the future. But what if it’s a survey? Say determining the career most suitable for an individual. Psychology is a science but the fact that it may or may not be correct even if it is based on statistics. These stats are based on similarities of peoples interests. But I see it as an evolution of numerology. or Psychology telling personality by measuring the head? But when the pattern is still unknown, still a mystery, does it still tie to a physical process? But even as scientists would you say that numbers without scientific meaning are always invalid? There is a proof in math that proves there is a significance to every number.
-
Does some numerology intersect with standard mathematics?
Well I saw an advertisement for a story on the news for sports analytics. I did not see it. But it showed simulations of football, much like the Madden football video game. But the again with the Ai are following each individual player for their path across the field on every play. Is such processing useful? Is it looking for patterns that aren’t? It has turned computational mathematics in numerology. But I am not convinced that numerology is completely merit less. I know the science community doesn’t accept it. But how do you differentiate it from a pattern we find in a mathematical series? We need a group consensus that other mathematicians also see it. It is based on rules that came before. But how are new rules found? I am not trying to convince you that patterns of events are a pattern will occur on a certain date or your birthday determines certain events. I’m just debating if there is some events that numerology explains or if it could be useful to find new patterns. In a pure scientific sense and not religious, Ai is a search for a pattern in every thing. Using numerology to find patterns could be purely scientific. Yes I don’t expect you to agree. But that is all a part of the debate. BTW my NCAA example is for basketball. Football is less dependent on single superstars. But do you think a computer could ever totally analyze football? I like what my local sports caster say that stats are good on paper but to learn the outcome you have to play the game. But do you agree that if analysis could predict everything it would ruin the game?
-
Does some numerology intersect with standard mathematics?
I’m not talking about describing everyone’s future based on their date of birth, but can certain types of numerology make you think twice if it’s legitimate? I mean are they wrong to look for mathematical patterns in everything? The same as we were trained to do. Here is my example: The NCAA Tournament bracket is impossible to predict every game. So let’s say the numerology way would have the same statistical chance as traditional maths team rankings. So let’s say the numerologists says they will take the player’s jersey numbers and determine the points scored by some complex assignment of winning potential versus the opposing team’s numbers. The traditional mathematician says that’s BS and says I’ll take each player’s jersey numbers and computer their average scoring by how long each jersey number stays in the game. Who wins the prediction? Are both approaches based on science? And is it so complex we can’t prove anything?
-
Is this a proper application of sesquation and quotation? My first new non Prime hypothesis. Can it be applied to multivariable equations?
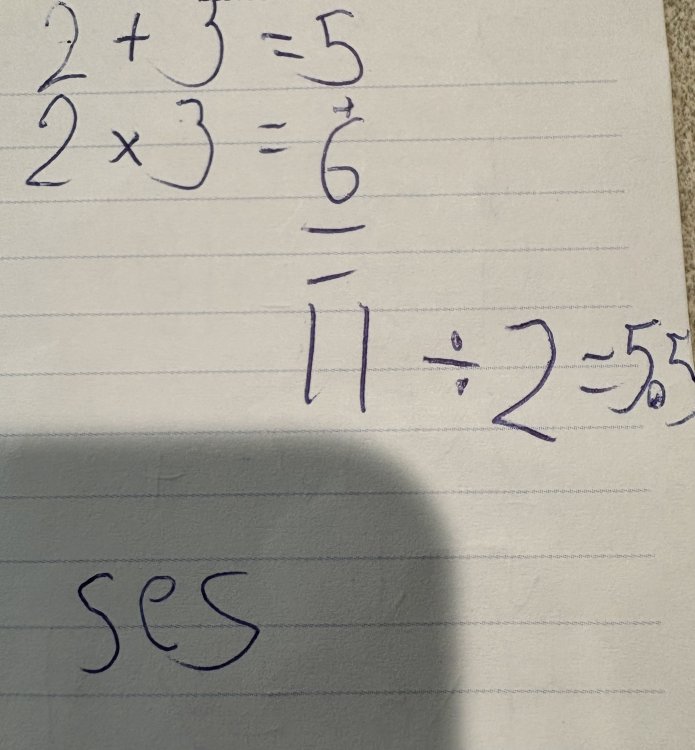
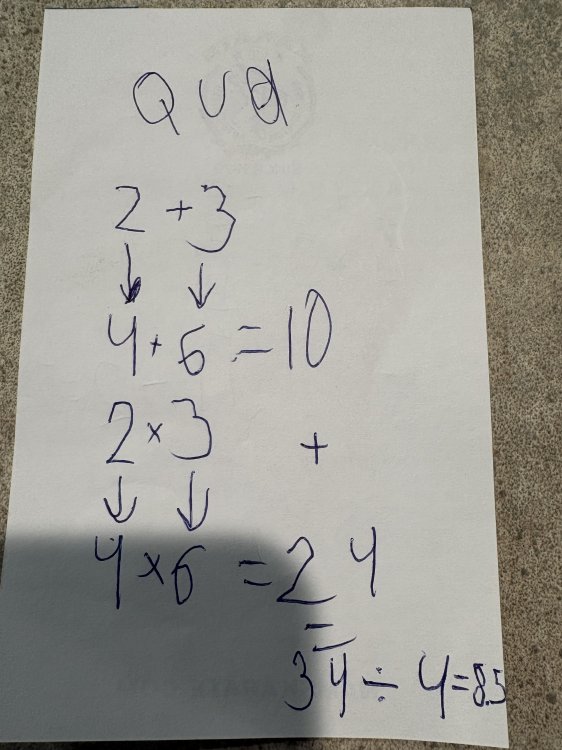
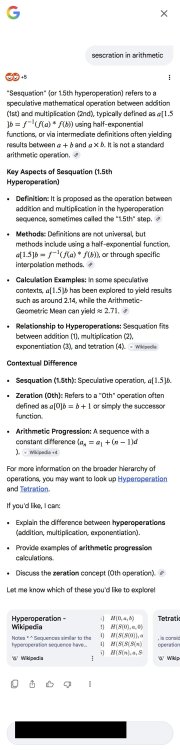
Very helpful video. Sesquation is in there. It is inspiring to see that we can put arithmetic in notation and find all of these patterns. I still don’t know how to spell quotation put I will post the picture below of both Sesquation and quotation.
-
Is this a proper application of sesquation and quotation? My first new non Prime hypothesis. Can it be applied to multivariable equations?
Well I never hear of sesquation either. It is first through 3rd grade arithmetic. When you search for it on Google you have to search “sesquation in arithmetic.” I don’t know how they teach some of these models to early elementary kids. Sometimes it seems like they should stick to how we learned when I was in school. Sometimes these learning methods are harder to understand than the actual math problem. But this one checks out and I believe it could be really powerful in a series or testing keys in cryptography. I listed the example my friend gave me above. The formatting with the space didn’t stay making it hard to read. But Sesquation and quotation are a real thing. We spend are our lives studying math and an elementary kids can solve patterns we can’t hope to. I believe kids can see infinite patterns they just lack the ability to describe them. The answers to the universe are there they just haven’t developed enough yet to communicate them. In a future post I will show the example my friend gave me.
-
Is this a proper application of sesquation and quotation? My first new non Prime hypothesis. Can it be applied to multivariable equations?
Ok here is a new hypothesis. Not related to Prime numbers, but cryptography itself. I know it is a long shot. But it is just a thinking exercise. I must thank my good friend Wyatt for explaining sesquation and quotation to me. Even though I am still trying to learn how to spell them. Yes I didn't make up sesquation or quotation. They are actually a thing in math. I have never encountered them before. So if anyone knows any links describing them please let me know. I know my hypothesis is off the wall, but I am quite serious. I reiterate that I did not make up sesquation and quotation. This is the first I heard of them. I am only pointing out these simple methods have uses in cryptography and also multivariable equations. Yes I know it sounds like nonsense, but a one-way-function is not just solving an impossible pattern. Instead it can be approached as solving for more than one unknown variable. Sesquation: 2+3 = 5 2*3 = 6 5+6 = 11 11/2 = 5.5 Quotation: 2+3 4+6 = 10 4*6 = 24 10+24=34 34/4 = 8.5 Patterns? Simple enough but does it describe slope, derivation, cryptography, or Trurl's Method? Taking the values from the last tabulation of Quotation above: 34-8.5 = 25.5 25-10 = 15.5 ______ 10+18.5 = 18.5 34-18.5 = 15.5 The Hypothesis is that the methods of sesquation and quotation can solve equations of multiple unknowns, if we know the end values of these methods. It could also be used to solve polynomial equations if we treat the variable in the polynomial equation as separate variables as the variable of the equation is raised to different power. For example for the polynomial method of the equation: (((pnp^2/ x ) + x^2) / pnp) = 1; replace x^2 with an unknown variable (say z) and plug it into quotation. Yes you have to know multiple answers of the quotation, but in cryptography the user is given many wrong tries compared to one right answer. There are many incorrect answers to work with. The goal is to see how the cypher effects the variables. This means if the user can find a pattern where the values produced randomness, then maybe the message could be solved. Yes I now that these patterns are hidden by cryptographic hash, but I am referring to pattern of the open source equation of the public key cryptography.
-
“The Star Mangled Spanner”
How do you know there is no credible threat? The media? Then it is psychological warfare. Trump’s reputation makes you think he is just bombing Iran to make America great again. I think it is strategic. Why let Iran build weapons till they are a significant threat? And what if you could reach a peaceful Iran? American Iranians were backing Trump. I know how the war looks and I don’t have access to military intelligence, but I don’t think Trump would start a war that would hurt the economy and kill thousands for no reason.
-
“The Star Mangled Spanner”
This of a war of perception. Iran is limited military, but if the people of the World view it the way the authors of the thread do it will lessen the effects of the campaign. Trump is largely responsible because his own reputation is based on his antics. But it could very well be this war is justified. We’d never know. It is just like any political debate with 2 opposing sides that both claim to be correct. And innocent people kill each other.
-
“The Star Mangled Spanner”
So I guess you guys don’t believe the nuclear material theory? I can’t understand the logic of this war. There must be something strategic or important. I mean why would Trump risk the economy unless he knew the economy would skyrocket after it ended? That is a risky gamble. And I don’t think he’d start a war based only on the fact that he has a stronger military. Because having more military might doesn’t mean your men don’t die and doesn’t mean swift victory. But as always this is my bs and comes with no scientific evidence.
-
Units for E = mc² ?
How many grams of astrophage is that?😉
-
Why graphics cards for AI and crypto currency?
Dell Precision Tower 7910 Workstation 2x E5-2620 V3 6C 2.4Ghz 16GB 2TB NVS310 No OS I bought 2 of theses refurbished workstations just below $1600. But they had a dual purpose: to crunch numbers and backup my workstation. The hardware is the same so I took open source free software and now have 3 computers with Win7. Adobe shut the servers of Creative Suite authentication. I have the software but supposedly you’d have to hack it to install software you paid for. But in the Mac comparison you say my Mac is faster than the Xeon. These Xeons are from 2015, so it seems so. So does this mean my M1 MacBook Pro is a better number cruncher? My nephew didn’t advise me on the Dell 7910’s but he said a dedicated computer with a lot of ram. My guess is that he meant a Linux os and small footprint. So is the Mac still faster even though it has more resources spread across the os? There is a lot of information here. I’ll follow up later. I’ll explain what I was trying to crunch. And why I am interested in neutral networks. I’m glad to hear you say they can’t do math patterns. But they can do iterations of combinations right? Anyway I want to be the one in control when I sit behind the computer.
-
Why graphics cards for AI and crypto currency?
I purchased 2 Xeon workstations for $800 each. They have 2 processors at 6 cores each. So that’s 12 cores. I am way behind on modern computers because I find the new computers lack useful software. That is my opinion that modern software is not useful. I know there is a lot of free software, but the user experience for purchased software is bad. But my figuring was to use the Xeon servers to crunch numbers. But a web search leads to AI and it says graphics cards are for bitcoin and Ai because the cores process smaller matrices faster. My question is why can’t a Xeon 12 cores crunch better than a graphics card? I’m sure Intel is wondering the same thing. There is a market for someone to solve Intel’s problem. I would like to see a return of older computer models of design. I want a computer that does what I tell it, not where I ok it to make changes to my computer that I don’t know where it is changing. Basically I want a Ai that can be trained on traditional processors. Of course I don’t have the knowledge of how a CPU or GPU actually work, but maybe it could be as simple as organizing tasks. I have done a little research and parallel processing is hard to adjust in simple programs. For instance when programming a math algorithm someone posted to a search that led to Reddit, it is more efficient to let the computer it self to decide how to utilize the cores. This again is the trend to let the computer do the thinking. BTW Mathematica now supports over 5 cores on a software reinstall. Do you think I spent my $1600 on the Xeon workstations wisely? I mean I can’t afford a graphics card that costs as much as a car. And I don’t want to crunch numbers blindly. By that I mean is I can edit Mathematica. I don’t want to train a GPU with my equations, have it write a program, and have it give me a number. Am I just old? Will future processors be built for something other than Ai?
-
Why graphics cards for AI and crypto currency?
I know the answer from Ai, but I don’t know the reason traditional processors can’t out perform a Nvida graphics card with 4 times the cores. I looked at on of the graphics cards and it was $5,000. But I think there is a demand here. If someone can utilize the traditional processors for better parallel processing than Nvida they would save the pc industry. Of course I am not on board with Ai. It makes changes to the computer while you program with it. But I can’t ignore it. I just don’t understand why traditional processors can’t be as efficient.